AWS Control Tower Integration Using CloudFormation
Overview
With Lacework and AWS Control Tower, enrolling a new AWS account now means security best practices and monitoring are automatically applied consistently across your organization. Account administrators can automatically add Lacework's security auditing and monitoring to AWS accounts seamlessly. All the required Lacework and AWS account configurations that allow access to AWS configuration and CloudTrail logs are managed for you by Lacework’s AWS Control Tower integration.
How It Works
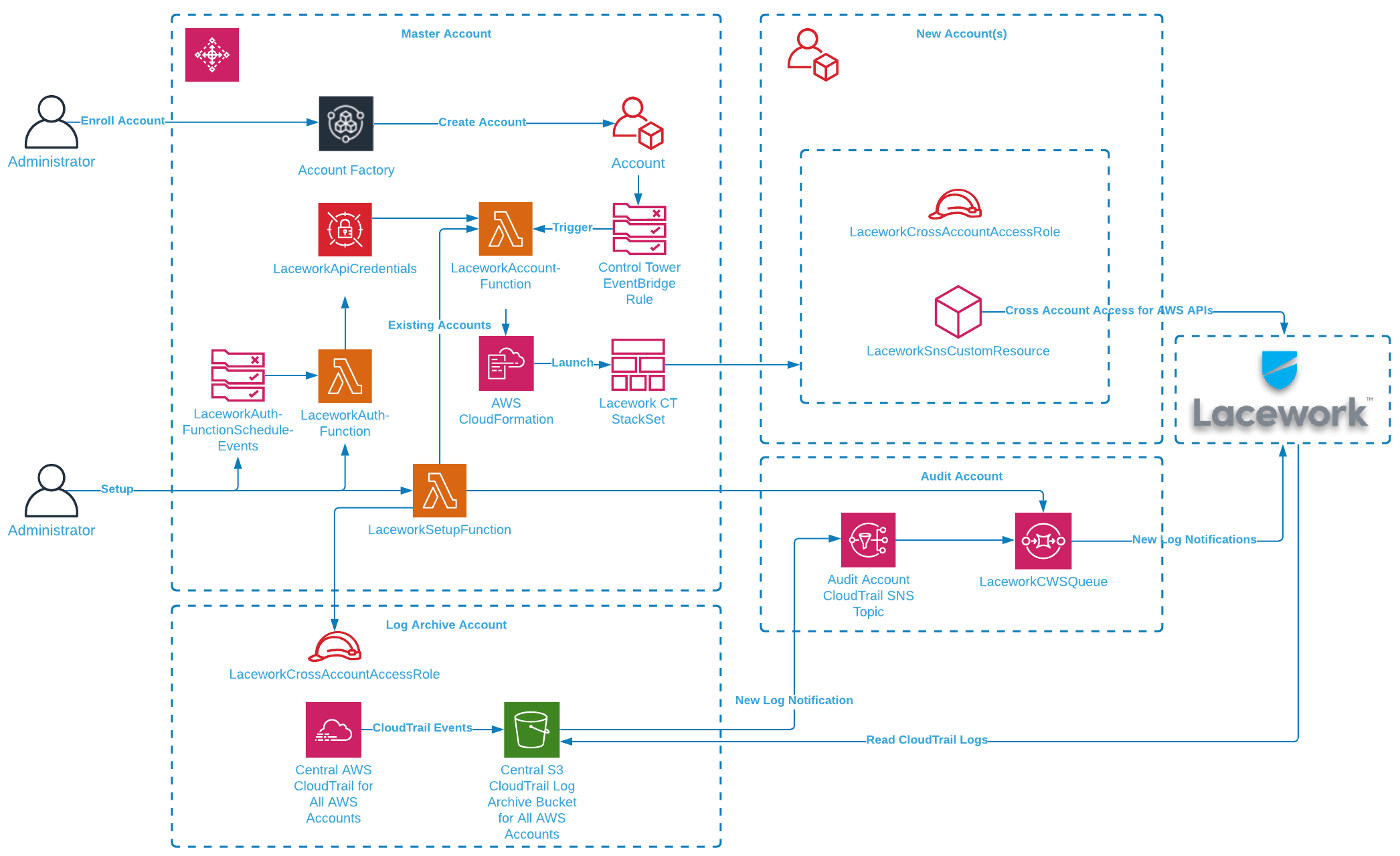
The Lacework AWS Control Tower integration audits and monitors AWS accounts in your AWS Control Tower Landing Zone. Your Landing Zone is your multi-account environment for which you can apply your governance, auditing and monitoring. On initial setup, the Lacework AWS Control Tower integration creates a new cross-account role in the Log Archive account and a new SQS queue is set up in the Audit account. The SQS queue lets Lacework receive notifications of new audit logs in S3 from the centralized CloudTrail that collects activity from all accounts. Lacework processes these logs for behavior analysis for all AWS accounts.
For new AWS accounts in your organization, AWS Control Tower Account Factory enables easy onboarding of new and existing AWS accounts which triggers the Lacework integration through a new account lifecycle event. A Lambda function launches a stack instance that creates a new cross-account role and allows Lacework to monitor the account via AWS APIs. The combination of CloudTrail log analysis and AWS API access lets Lacework check your cloud activity and AWS configuration to detect security misconfigurations and anomalous behavior.
note
The current solution only works for Landing Zone 3.0+. If you are using Landing Zone 2.X, contact your Lacework Customer Success Manager for further assistance.
Prerequisites
You need the following prerequisites to implement the Lacework AWS Control Tower integration.
- AWS Control Tower with a Landing Zone. For information about setting up an AWS Control Tower landing zone, see Getting Started with AWS Control Tower in the AWS Control Tower User Guide.
- Administrator privileges in the AWS Control Tower management account.
- A Lacework Cloud Security Platform SaaS account.
Deployment Scenarios
1. Without Lacework Organization
If the Lacework Organization feature is not enabled, all AWS accounts go under the main Lacework account by default. Leave the Single Sub-Account Configuration and Organization Configuration sections blank in the CloudFormation stack parameters.
2. Single Lacework Sub-Account with Lacework Organization
If the Lacework Organization feature is enabled, you can specify a Lacework Sub-Account for which all AWS accounts are added. This is specified in the Single Sub-Account Configuration section in the Lacework Sub-Account Name field (see below) in the CloudFormation stack parameters.
note
This scenario only works with Configuration Integration Type.
3. AWS Organizational Units (OUs) to Lacework Sub-Account Mapping with Lacework Organization
note
- You must have the Lacework Organization feature enabled.
- When naming the OUs, ensure to not include spaces in the names (hyphens are allowed).
- Dev Infra ❌
- Dev-Infra ✅
- Dev Infra ❌
The below tabs describe what will happen during the deployment for Config and CloudTrail.
Config CloudTrail
When creating or deleting AWS OUs, ensure that you use the recommended AWS Control Tower methods. Making updates to AWS accounts outside of AWS Control Tower may cause issues. You will also need to re-run the Lacework Control Tower integration for those changes to ensure that Lacework monitors each AWS account in the correct Lacework Sub-Account.
Below is an example of using Lacework Control Tower integration:
Example
- (1st level)
- OU=Tech
- AWSAccount 1 (techaws)
- OU=IT
- AWSAccount 2 (itcloud)
- OU=Marketing (it has sublevels)
- OU=prod
- AWSAccount 3 (marketingprodUS)
- AWSAccount 4 (marketingprodEU)
- OU=dev
- AWSAccount 5 (marketingdev1)
- AWSAccount 6 (marketingdev2)
If you create a Lacework Sub-Accounts named Tech and Marketing, and want to use Lacework Control Tower integration, specify the following comma-separated arguments to the Cloudformation template in the Organization Configuration (Optional) field as Tech,Marketing.
As a result, we’ll integrate AWS Configuration settings as follows:
- LW subAccount Tech
- AWSAccount 1 (techaws)
- LW subAccount Marketing
- AWSAccount 3 (marketingprodUS)
- AWSAccount 4 (marketingprodEU)
- AWSAccount 5 (marketingdev1)
- AWSAccount 6 (marketingdev2)
AWSAccount 2 (itcloud).Below is an example of using Lacework Control Tower integration:
Example
- (1st level)
- OU=Tech
- AWSAccount 1 (techaws)
- OU=IT
- AWSAccount 2 (itcloud)
- OU=Marketing (it has sublevels)
- OU=prod
- AWSAccount 3 (marketingprodUS)
- AWSAccount 4 (marketingprodEU)
- OU=dev
- AWSAccount 5 (marketingdev1)
- AWSAccount 6 (marketingdev2)
Once the Control Tower CFT deployment is done, the customer is then asked to perform an Organizational Cloudtrail integration with the following mappings:
{
"defaultLaceworkAccountAws": "lw_account_1",
"integration_mappings": {
"Tech": {
"aws_accounts": [
"1"
]
},
"Marketing": {
"aws_accounts": [
"3",
"4",
"5",
"6"
]
}
}
}
Any AWS accounts that are not included in the mapping will have their CloudTrail logs sent to the default Lacework Sub-Account.
To upload a mapping file, see Setup of Organization AWS CloudTrail Integration for more information.
Installing the Lacework AWS Control Tower Integration
1. Generate a Lacework API Access Key
- In your console, go to Settings > Configuration > API keys.
- Click on the + Add New button in the upper right to create a new API key.
- Provide a name and description and click Save.
- Click the download button to download the API keys file.
- Copy the keyId and secret from this file.
2. Log in to your AWS Control Tower Management Account
- Log in to AWS Control Tower management account.
- Select the AWS region where your AWS Control Tower is deployed.
3. Deploy the Lacework AWS Control Tower Integration with CloudFormation
Click the following Launch Stack button to go to your CloudFormation console and launch the AWS Control Integration template.

For most deployments, you need only Basic Configuration parameters.
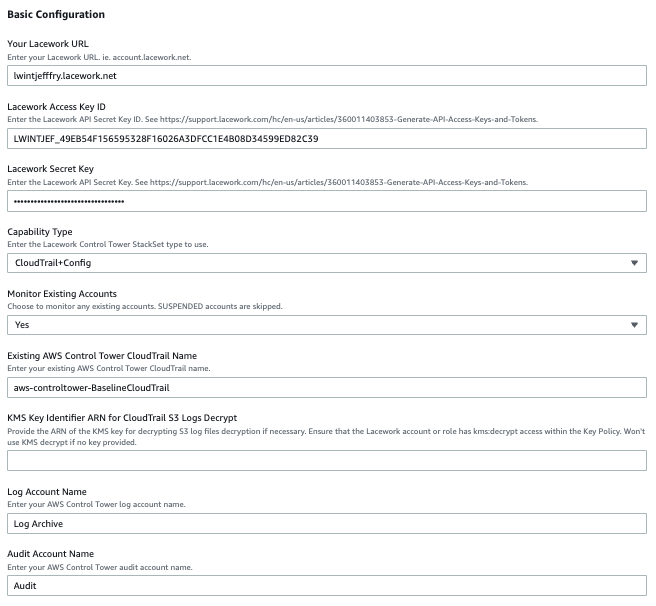
Specify the following Basic Configuration parameters:
Enter a Stack name for the stack.
Enter Your Lacework URL.
Enter your Lacework Access Key ID and Secret Key that you copied from your previous API keys file.
For Capability Type, the recommendation is to use CloudTrail+Config for the best capabilities.
Choose whether you want to Monitor Existing Accounts. This sets up monitoring of ACTIVE existing AWS accounts.
Enter the name of your Existing AWS Control Tower CloudTrail Name.
If your CloudTrail S3 logs are encrypted, specify the KMS Key Identifier ARN. Ensure that you update the KMS key policy to allow access to the Log account cross-account role used by Lacework. Add the following to the key policy.
"Sid": "Allow Lacework to decrypt logs",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::<log-archive-account-id>:role/<lacework-account-name>-laceworkcwssarole"
]
},
"Action": [
"kms:Decrypt"
],
"Resource": "*"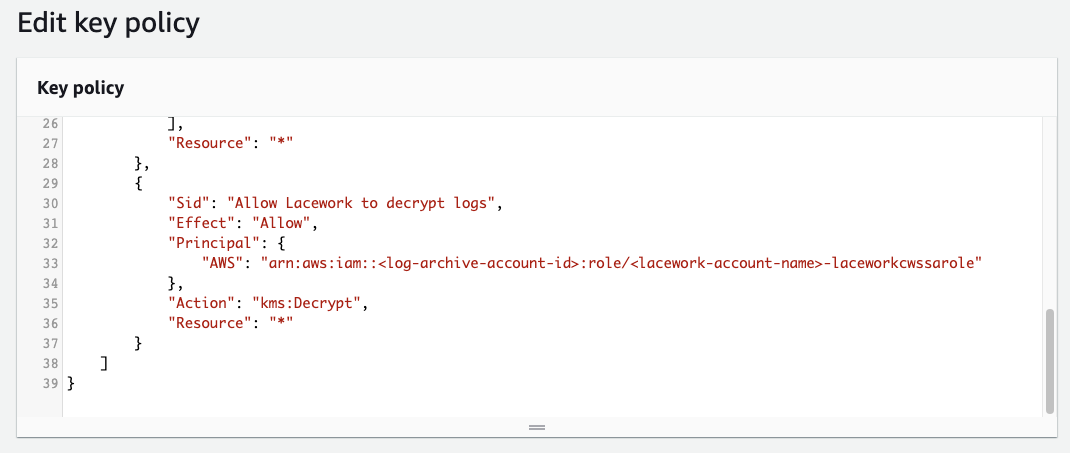
Update the Control Tower Log Account Name and Audit Account Name if necessary.
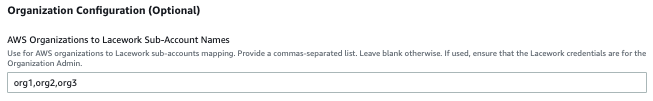
If using AWS organization units to Lacework Sub-Account mapping, specify a comma-separated lists of organization names in the Organization Configuration section in the AWS Organizations to Lacework Sub-Account Names field. AWS accounts are added to the appropriate Lacework Sub-Accounts based on this AWS OU-to-Lacework Sub-Account name mapping. AWS OU names and Lacework Sub-Account names must match. AWS accounts not in the specified organization units are not added to Lacework.
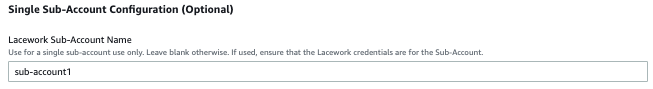
If using a single Lacework sub-account for all AWS accounts, specify a Lacework Sub-Account for which all AWS accounts will be added. This is specified in the Single Sub-Account Configuration section in the Lacework Sub-Account Name field.
Click Next through to your stack Review.
Accept the AWS CloudFormation terms and click Create stack.
4. CloudFormation Progress
- Monitor the progress of the CloudFormation deployment. It takes several minutes for the stack to create the resources that enable the Lacework AWS Control Tower Integration.
- When successfully completed, the stack shows
CREATE_COMPLETE.
5. Validate the Lacework AWS Control Tower Integration
- Log in to your Lacework Cloud Security Platform console.
- Go to Settings > Integration > Cloud Accounts.
- You should see a list of AWS accounts that are now being monitored by Lacework. The Cloud Account column values correspond to the AWS Account IDs.
Once the Control Tower CloudFormation deployment is competed, you need to setup an Setup of Organization AWS CloudTrail Integration and upload a mapping file. Any AWS accounts that are not included in the mapping will have your CloudTrail logs sent to the default Lacework Sub-Account.
Remove the Lacework AWS Control Tower Integration
To remove the Lacework AWS Control Tower Integration, simply delete the main stack. All CloudFormation stacksets, stack instances, and Lambda functions will be deleted.
note
Lacework will no longer monitor your AWS cloud environment.
Troubleshooting
The following sections provide guidance for resolving issues with deploying the Lacework AWS Control Tower integration.
Common Issues
Ensure the Existing AWS Control Tower CloudTrail Name is correct. You can verify this on your AWS CloudTrail Dashboard.
Ensure that your Log Archive and Audit account names are correct and these accounts are
ACTIVE.If you are using the Lacework Organization feature to manage your accounts, specify the correct Sub-Account name, API key ID, and secret key.
If Lacework returns an S3 access error for the CloudTrail account and a KMS key is used, ensure you update the KMS key policy to allow access to the Log account cross-account role used by Lacework.
"Sid": "Allow Lacework to decrypt logs",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::<log-archive-account-id>:role/<lacework-account-name>-laceworkcwssarole"
]
},
"Action": [
"kms:Decrypt"
],
"Resource": "*"
Events and Logs
CloudFormation Events
You can monitor the CloudFormation events for the Lacework AWS Control Tower integration stack. Events may reveal issues with resource creation. The Lacework AWS Control Tower integration stack launches a main stack and three stacksets:
Main Deployment Stack:
- control-tower-integration.template.yml - Main stack that deploys all resources: IAM roles, access token credentials, IAM roles, SQS queues, Lambda functions and the stacksets below.
Centralized CloudTrail Cloud Account in Lacework: (Applied once during initial deployment)
- lacework-aws-ct-audit.template.yml -> Lacework-Control-Tower-CloudTrail-Audit-Account-Lacework account - Creates a stack instance in the Audit account.
- lacework-aws-ct-log.template.yml -> Lacework-Control-Tower-CloudTrail-Log-Account-Lacework account - Creates a stack instance in the Log account.
Config Cloud Account in Lacework: (Applied for each AWS account)
- lacework-aws-cfg-member.template.yml -> Lacework-Control-Tower-Config-Member-Lacework account - Creates a stack instance in each AWS account.
Examining these stacksets for operation results, stack instance results and parameters may also provide debug information.
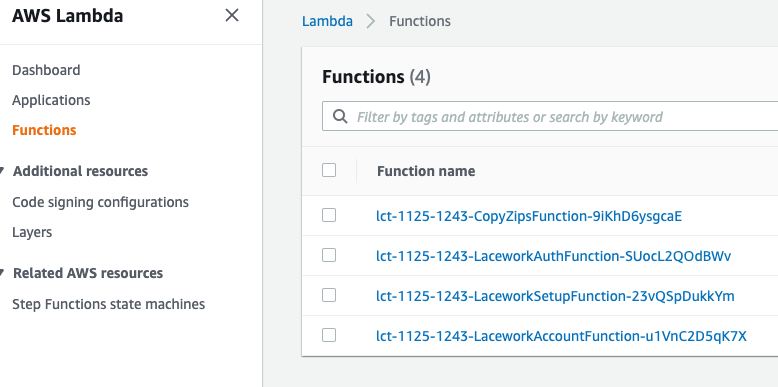
Lambda Function CloudWatch Logs
Two main Lambda functions are used to manage accounts. LaceworkSetupFunction manages the initial deployment of the integration. LaceworkAccountFunction manages setting up existing and new accounts. Both Lambda functions provide extensive debug messages that can be seen in their respective CloudWatch log streams.